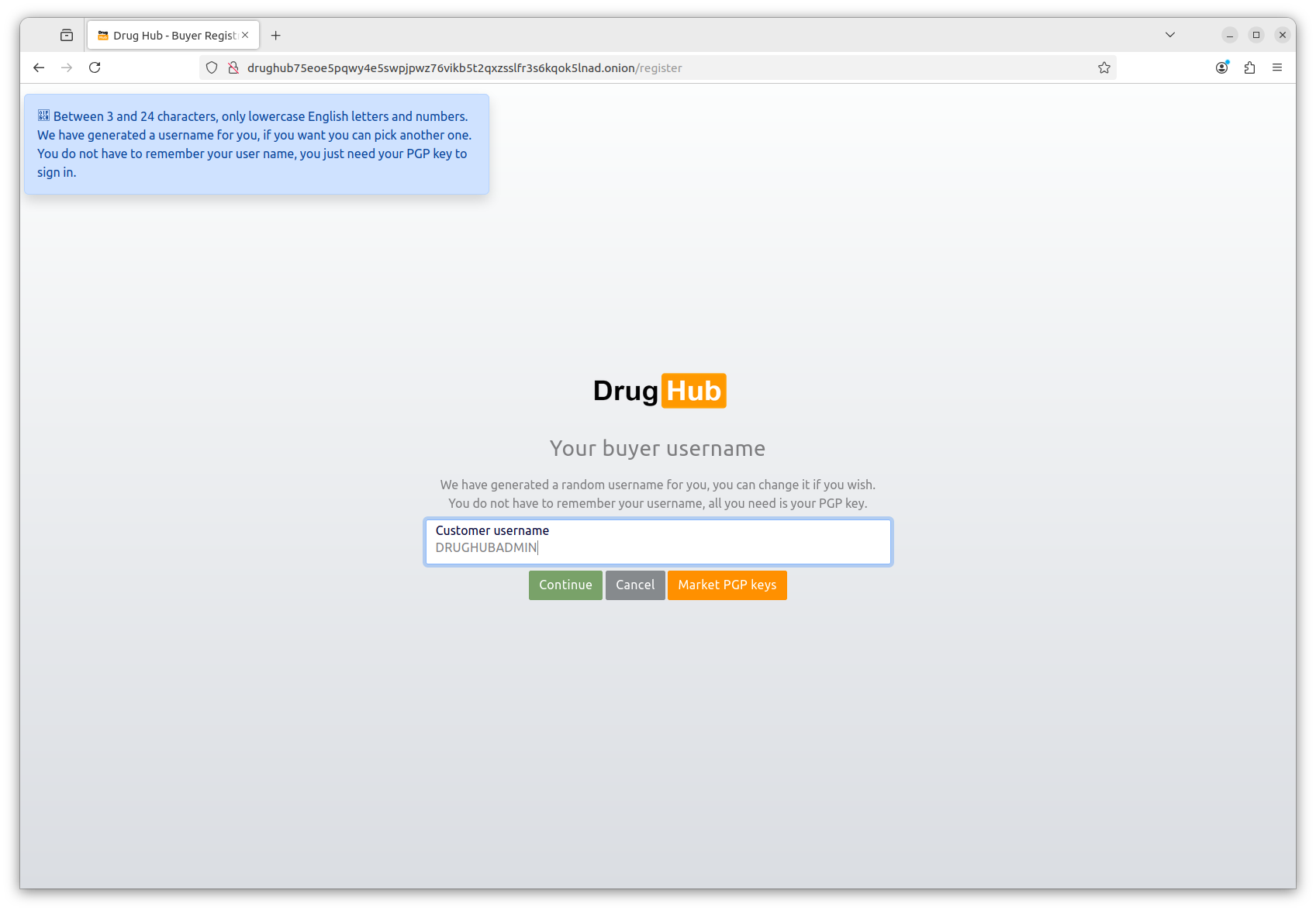
Generate a 4096-bit PGP key and upload to Drughub
Drughub uses passwordless PGP authentication. Your private key is your login credential. Your public key is what the platform stores. This means: if you lose the private key, you lose account access permanently. There is no "forgot password" flow — by design.
Generate a key with GnuPG:
gpg --full-generate-key
Choose RSA, 4096-bit key size. Set an expiry of one to two years — you can extend it before it expires. Use a strong passphrase stored in KeePassXC. The UID (name/email) can be anything — it won't be shown publicly on Drughub. Many users use a pseudonymous handle.
Export your public key:
gpg --armor --export YOUR_KEY_ID > drughub_public.asc
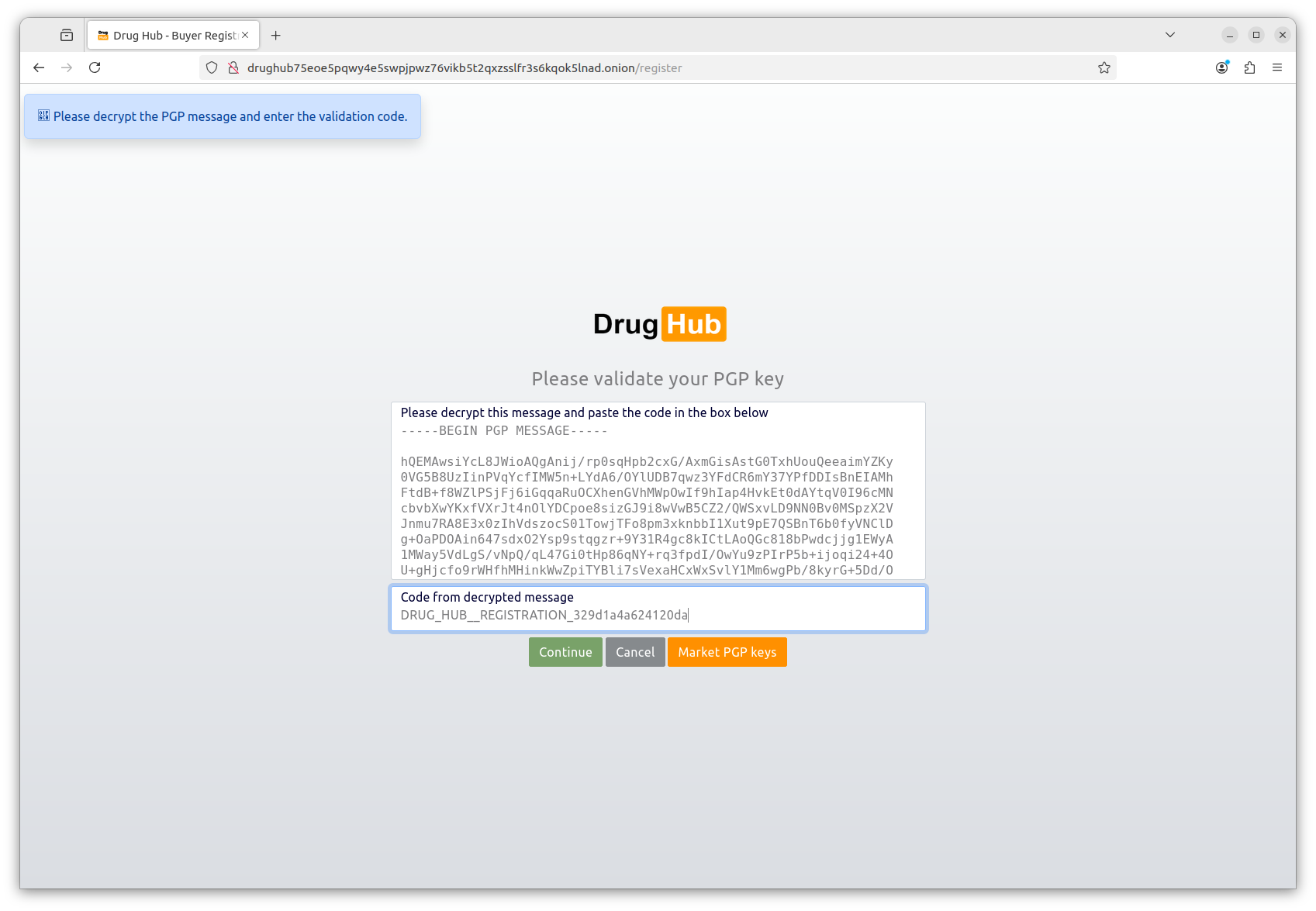
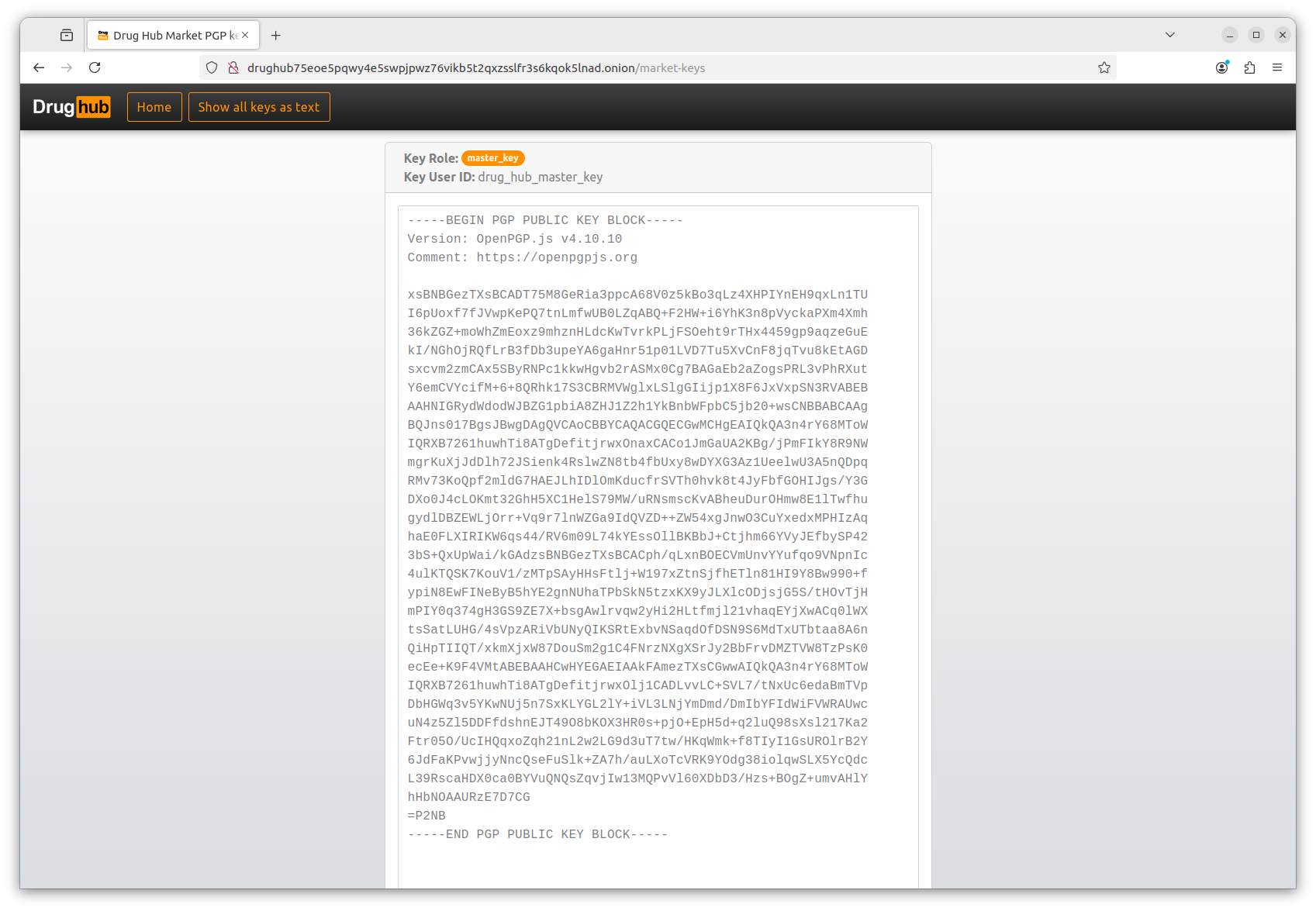
Open drughub_public.asc, copy the entire block (including the -----BEGIN PGP PUBLIC KEY BLOCK----- header), and paste it into the Drughub registration PGP field.
Back up your private key immediately. Export it, encrypt the export, and store it offline — on a USB drive in a separate location, or on paper using the gpg --gen-revoke revocation certificate. Losing the key means losing the account. No recovery path exists.