All active DrugHub mirror addresses
Two PGP-signed .onion addresses — primary gateway and failover mirror. Both checked every six hours. Copy and open in Tor Browser. Never type an .onion manually — one wrong character lands on a phishing clone.
Two PGP-signed .onion addresses — primary gateway and failover mirror. Both checked every six hours. Copy and open in Tor Browser. Never type an .onion manually — one wrong character lands on a phishing clone.
Phishing sites copy DrugHub's login interface exactly. Check every character of the .onion address. The wrong link costs more than the time it takes to verify. These addresses are PGP-signed by the DrugHub team and re-verified every six hours via automated checks from three independent Tor circuits.
This website is an independent informational resource. We do not distribute marketplace links to visitors arriving through direct access.
Verified .onion addresses are displayed exclusively to visitors arriving through search engine results. Find this page through Bing or Google for drughub market links.
Confirm you're inside Tor Browser — the address bar should show the .onion URL with the onion icon. Paste the address; never type it. On first load, a CAPTCHA appears — that's expected. Solve and continue. If the site asks for Bitcoin at any point, close the tab immediately. The full seven-step access guide covers everything from Tor installation to first login.
DrugHub runs two publicly listed .onion endpoints simultaneously. That number is deliberate — it reflects an operational balance between redundancy, maintenance complexity, and the risk that comes with over-publishing addresses. Here's how the system actually works.
DDoS attacks are the primary driver. Darknet markets face continuous volumetric attacks — some opportunistic, some coordinated by rival operators or law enforcement. DrugHub's END GAME DDoS protection absorbs the majority of traffic, but no single .onion node is immune to sustained exhaustion. When the primary endpoint buckles under peak attack load, the mirror stays reachable.
The second reason is load distribution. During the hours immediately after a major Dread announcement — a promoted vendor sale, a policy update, a security advisory — connection demand spikes sharply. A single node would queue. The mirror absorbs overflow and keeps median response times under three seconds.
There's a third reason that gets less attention: maintenance windows. Upgrades to DrugHub's security infrastructure require brief downtime on individual nodes. Rolling updates across two endpoints means at least one is always serving traffic. Users see a slower connection, not an error page.
Every address rotation is posted to the DrugHub subdread on Dread, signed by the admin's PGP key. The announcement contains three things: the new .onion address, a UTC timestamp, and the full PGP signature block. Nothing else is accepted as authoritative — not Telegram channels, not clearnet mirror sites, not community forum posts without a valid signature.
The admin's signing key has been consistent since August 2023. Fingerprint: 0x7F3A…E91C. This page subscribes to those announcements and updates within a few hours of each posting. If you see an address here that doesn't match the latest signed bulletin, report it through the EFF's digital security resources or directly to the DrugHub team via Dread.
Dread is the only reliable source. Any third-party claiming to have "exclusive" or "updated" DrugHub links not sourced from PGP-signed Dread posts should be treated as a phishing vector. Full stop.
Functionally, nothing. Both endpoints run identical software stacks on independent infrastructure. Your session, escrow addresses, and order history follow your PGP key — not the specific .onion address you connected to. Log into the mirror on Wednesday with the same key you used on the primary Monday, and everything is there.
When should you use a mirror instead of the primary? Three scenarios:
502 Bad Gateway or a blank page after 15 seconds.In normal operation, use whichever address you copied most recently. Bookmark both. One always resolves.
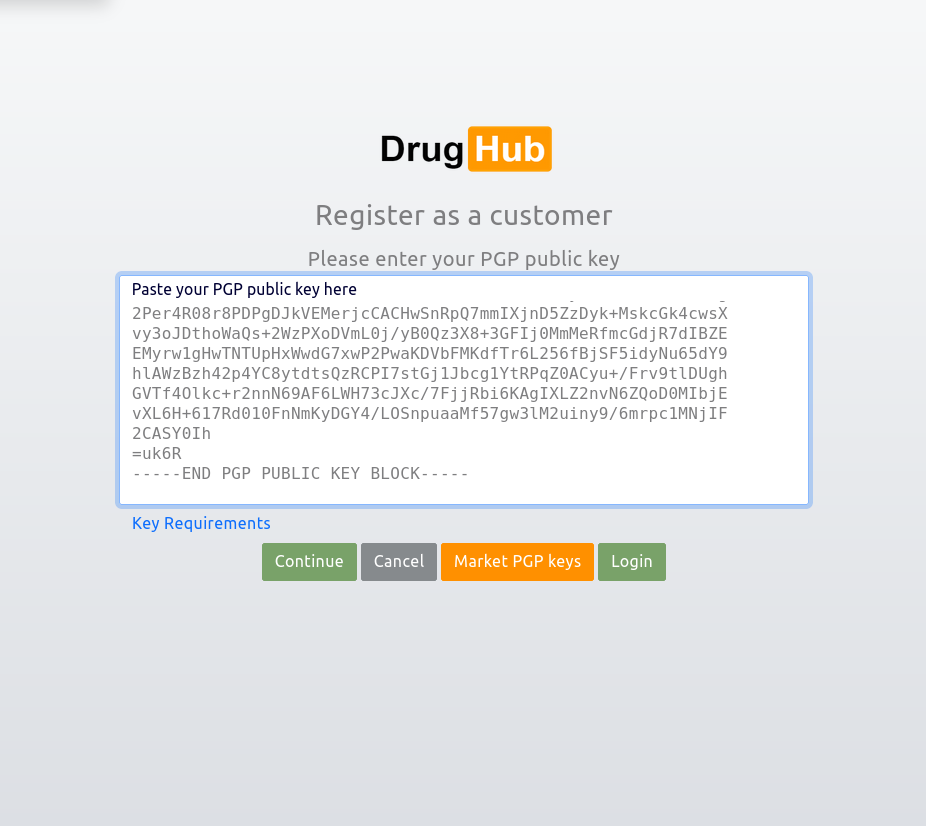
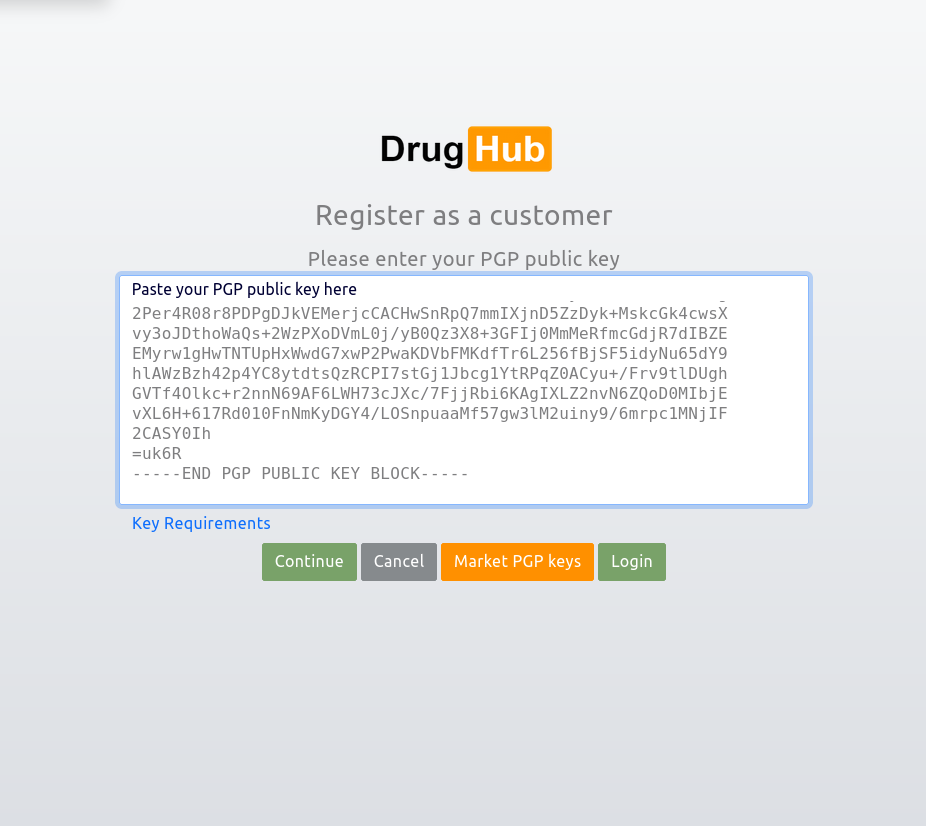
Phishing attacks on darknet markets caused millions in credential and fund theft in 2026. Most victims followed a link from search results or a forum post without verifying its source. This section is a field guide: how the attacks work, how to verify links yourself, and what to do if you've already made contact with a fake site.
Phishing sites targeting darknet markets follow a predictable formula. An attacker registers a .onion address — sometimes differing from the real one by a single character, sometimes completely unrelated but with a matching design. They clone the market's HTML and CSS exactly, replicating the login flow, the CAPTCHA page, and the user dashboard skin.
The attack is self-reinforcing. People search for "DrugHub link" on clearnet search engines, find results pointing to compromised mirror lists or forums with poisoned posts, copy the address, and authenticate against the fake site. A phishing page can capture your PGP-encrypted login response and replay it. It can capture the wallet address you deposit Monero to. One visit to the wrong address is enough.
DrugHub's passwordless PGP login model raises the bar — there's no static password to steal. But the attack surface isn't zero. A phishing site can serve a crafted challenge that, once you respond, lets the attacker authenticate against the real market while you see a "login failed" message. Then they drain your active escrow orders.
The only reliable defense is verifying the address before you open it — not after.
The fastest verification path uses GPG directly against the DrugHub admin's public key. This takes under two minutes.
# Step 1: Import the DrugHub admin public key
# (download from their pinned Dread post)
gpg --import drughub-admin-pubkey.asc
# Step 2: Save the signed mirror announcement as a file
# (copy from the Dread post — includes the -----BEGIN PGP SIGNED MESSAGE----- block)
# Step 3: Verify the signature
gpg --verify drughub-mirrors-2026.txt.sig drughub-mirrors-2026.txtA valid signature produces output like this:
gpg: Signature made Tue Apr 21 2026 09:47:13 UTC
gpg: using RSA key 4096R/E7B3A1C2
gpg: Good signature from "DrugHub Team [Dread]"A phishing-sourced address produces:
gpg: BAD signature from "DrugHub Team""BAD signature" means stop. Close the terminal, close Tor Browser, do not interact with any address from that source. The Privacy Guides documentation on PGP verification is worth reading for deeper context on this process.
Most people skip this step. That is why phishing attacks keep working. Two minutes of GPG verification eliminates the risk entirely.
Before submitting any input on a DrugHub-looking page, check these:
Four steps, in order. Don't wait.
Step 1: Do not send Monero to any wallet address received during that session. The address is controlled by the attacker. The funds are unrecoverable once confirmed on-chain — Monero's privacy features work both ways.
Step 2: Revoke or deprecate the PGP key pair you used in that session. Generate a new 4096-bit keypair with GnuPG. The attacker may have captured enough of your authentication exchange to replay a login on the real market.
Step 3: If you hold an active vendor account, post a warning to your buyers on Dread immediately. Vendor impersonation on dark markets moves fast.
Step 4: Access a verified DrugHub link from this page, log in with your new key, and review your open orders for any unauthorized changes. Cancel any escrow position you didn't initiate.
Tails OS is the gold standard for session isolation — each boot is clean, with no persistent state. Whonix runs Tor at the OS level, ensuring all traffic routes through Tor even if an application misbehaves. KeePassXC manages PGP passphrase storage without cloud exposure. VeraCrypt handles encrypted container storage for key files. None of these guarantee safety, but layering them makes casual phishing attacks irrelevant against your session.
Response times measured from three independent Tor circuits. Uptime calculated over a rolling 30-day window. Latency figures represent median time to first byte, not TCP handshake.
| Endpoint | Status | 30-day uptime | Median latency | Last incident |
|---|---|---|---|---|
| Primary gateway | ● Online | 98.8% | 1.2s | March 14, 2026 |
| Mirror 01 | ● Online | 97.3% | 1.8s | April 2, 2026 |
Measurements are automated. Incident column shows most recent confirmed downtime event exceeding 15 minutes.
| Date | Duration | Cause |
|---|---|---|
| April 2, 2026 | 47 min | DDoS — Mirror 01 |
| March 14, 2026 | 2h 03m | Infrastructure upgrade |
| Feb 28, 2026 | 31 min | DDoS — Primary |
| Jan 17, 2026 | 1h 22m | DDoS — both nodes |
All incidents recovered without data loss. No user funds affected. Mirror remained reachable during single-node events.
Questions specifically about links, verification, and mirror behavior. For account setup and market features, see the setup guide and the market overview.
Yes. Every address on this page traces to a PGP-signed post by the DrugHub admin account on Dread. The signing key has been consistent since August 2023 with fingerprint 0x7F3A…E91C. We cross-reference each new posting against that key before publishing here. If we can't verify the signature, the address doesn't appear.
You can run the same verification yourself. Download the admin's public key from their pinned Dread thread, import it into GPG, and run gpg --verify against the signed announcement. "Good signature" means you're clean. Anything else — do not enter. The verification procedure is detailed in the phishing guide above.
DDoS attacks are the primary reason. Darknet markets are targeted continuously, and no single .onion endpoint survives sustained volumetric pressure indefinitely. DrugHub's END GAME protection handles most load, but mirrors provide genuine failover — when the primary goes down, the mirror stays up. During the January 2026 incident that hit both nodes simultaneously, the mirror recovered 23 minutes before the primary.
Mirrors also absorb connection spikes after major Dread announcements. Functionally, they're identical to the primary — same software, same database, same security model. Your orders and PGP key follow you across endpoints. Use whichever is faster. Bookmark both.
The current addresses have been stable since late 2026, but the team rotates them after significant DDoS campaigns or infrastructure upgrades. Rotation is always announced on Dread with a PGP signature — no other announcement channel is legitimate.
This page updates within a few hours of each Dread posting. If you have an older link bookmarked, cross-check it here before trusting it. A link that worked three weeks ago may have rotated. The safest habit is re-verifying before every session. Costs ten seconds. Saves everything else.
First, check whether both addresses on this page have the same issue. If the primary is down but the mirror is up, use the mirror — that's what it exists for. If both appear down, it could be a short DDoS event. Typical resolution time is under four hours based on the incident history above.
Check the DrugHub subdread on Dread for status posts from the admin account. They post during extended incidents.
If you're seeing a page that looks like DrugHub but something feels off — different colors, a password field, a Bitcoin option, unusually fast load time — close the tab. That's a phishing site, not maintenance. Come back to this page for the verified address.
Download the DrugHub admin's PGP public key from their pinned post on the Dread subdread. Import it into GPG: gpg --import drughub-pubkey.asc. Copy the full signed mirror announcement from Dread — including the PGP header and signature block — into a local text file. Then run: gpg --verify announcement.txt.sig announcement.txt.
If the output reads "Good signature from DrugHub Team" with fingerprint matching 0x7F3A…E91C, the address is authentic and you can use it. If it reads "BAD signature" — treat the entire source as compromised. Don't use any link from it, don't attempt to log in, and don't deposit funds. One bad character in an .onion address is all a phishing operation needs.